How a Cyber Background Check Can Protect Your Business from Security Threats
Introduction: The Growing Need for Cybersecurity in Business
As businesses become more reliant on digital technology, the threat of cyberattacks grows exponentially. Cybersecurity breaches can lead to massive financial losses, loss of consumer trust, and reputational damage. One of the most effective ways to minimize these risks is through a Cyber Background Check. This article will explore how implementing these checks can protect your business from security threats, enhance your hiring processes, and ensure you hire trustworthy individuals with a strong security mindset.
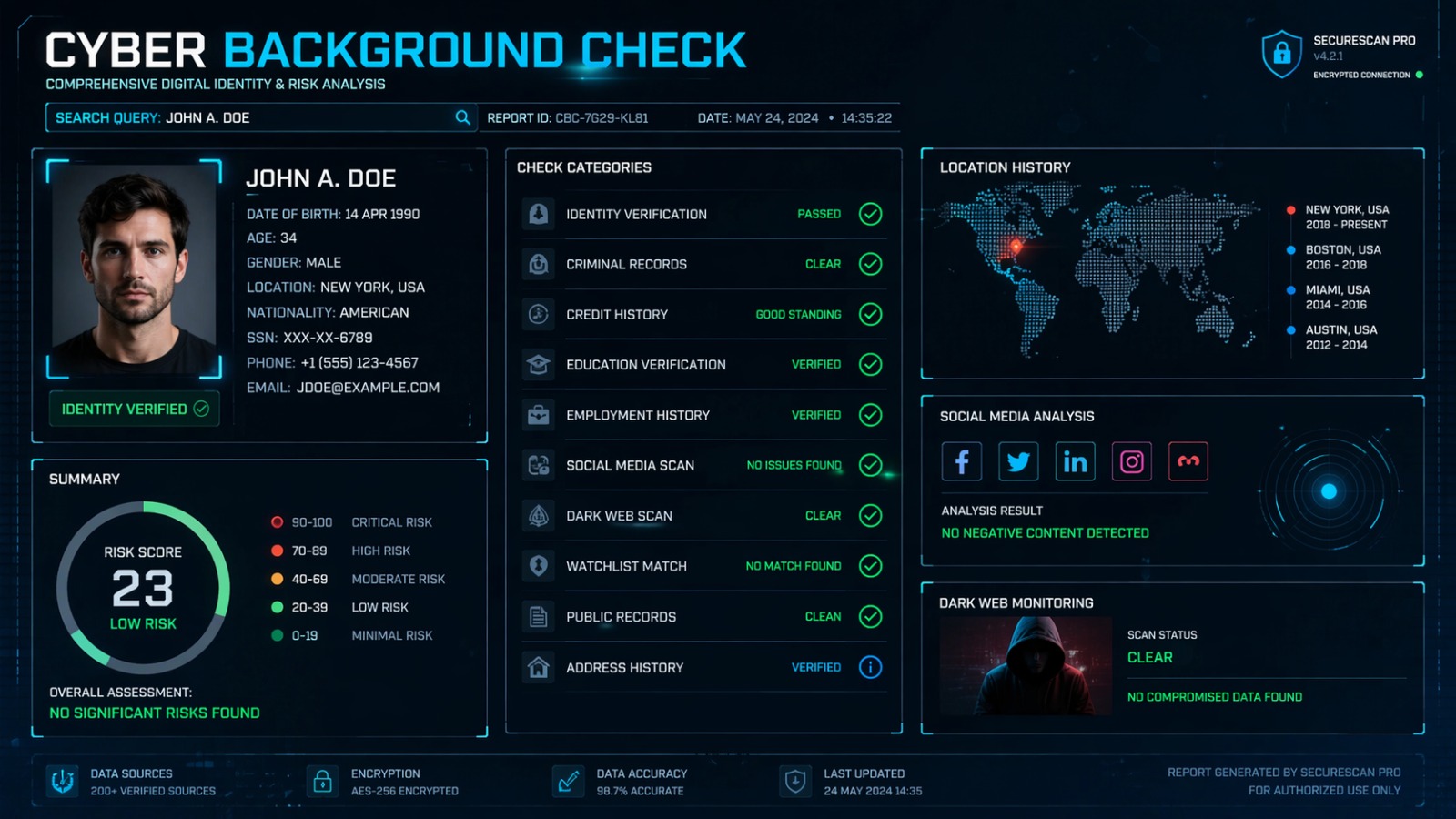
What is a Cyber Background Check?
A Cyber Background Check is a detailed examination of an individual’s online and digital activities to assess their potential risks to an organization’s cyber infrastructure. It goes beyond traditional background checks, which focus on criminal records, to evaluate an individual’s behavior and activity in the online space. This check typically includes reviewing past hacking activity, involvement in cybercrime, social media behavior, and overall online presence.
It helps employers to verify that employees, especially those in positions with access to sensitive data or critical systems, do not have any troubling history that could pose a threat to the business. The goal of this background check is to safeguard sensitive information and ensure that the right individuals are hired for security-sensitive positions.
Why a Cyber Background Check is Crucial for Your Business
With the increase in digital transformation, companies are storing vast amounts of sensitive customer data, financial information, and intellectual property. These assets are prime targets for cybercriminals. However, the threat doesn’t just come from external hackers; often, employees or contractors with access to critical data can be the source of a breach. A Cyber Background Check acts as a shield against these internal threats by ensuring that your employees have no history or tendency towards digital misconduct or cybercrime.
Here are some specific reasons why a Cyber Background Check is vital for protecting your business:
- Prevention of Insider Threats: Many cyberattacks originate from insiders, whether due to malice or negligence. A background check can help identify individuals with a history of questionable online behavior, helping to prevent internal breaches.
- Ensuring Data Security: Your business’s most valuable asset may be the data it holds. Ensuring that individuals with access to this data have clean cyber backgrounds is critical in maintaining your data security.
- Compliance and Regulatory Standards: Many industries, such as finance and healthcare, require businesses to implement stringent background checks on their employees. A Cyber Background Check helps ensure compliance with these regulations.
How Cyber Background Checks Work: Key Areas of Evaluation
A Cyber Background Check involves several crucial steps designed to provide a comprehensive view of an individual’s online behavior. Some key areas evaluated include:
1. Social Media Activity
Social media platforms offer a window into a person’s online persona. A Cyber Background Check involves analyzing an individual’s social media history to determine if there are any red flags, such as connections to extremist groups, inappropriate or harmful posts, or a pattern of behavior that may be considered risky for the company. Social media activity also helps identify potential conflicts of interest, online harassment history, or involvement in cyberbullying.
2. Past Involvement in Cybercrime
A crucial part of the check is looking for any past involvement in cybercrimes such as hacking, data theft, or online fraud. If an individual has been convicted or suspected of such crimes, they pose a significant risk to your business’s cybersecurity. The Cyber Background Check also involves analyzing their online behavior to identify any patterns that suggest they may be involved in cybercriminal activities.
3. Digital Footprint
An individual’s digital footprint can reveal a lot about their online behavior, such as the websites they visit, their involvement in online communities, or their subscriptions to online forums related to cybercrime. Analyzing this footprint helps to uncover any red flags or behaviors that may indicate that a candidate could pose a risk.
4. Email and IP Address Analysis
Cybercriminals often use email addresses and IP addresses to carry out illicit activities. By analyzing these data points, companies can identify any suspicious activity linked to hacking, phishing, or fraudulent activity. If an individual has a history of using email addresses linked to cybercrimes, they may be flagged during the background check process.
5. Review of Previous Employers and Job Roles
In certain cases, a Cyber Background Check will include verifying an individual’s previous employers and job roles, especially if they worked in positions with access to sensitive information or large IT systems. If an individual has a history of being fired or reprimanded for security breaches or poor cyber hygiene in previous roles, they may not be suitable for the position.
The Benefits of Cyber Background Checks for Hiring Managers
For hiring managers, Cyber Background Checks serve as an essential tool to ensure that candidates possess the necessary integrity, competence, and trustworthiness. Let’s explore some of the primary benefits of conducting these checks:
1. Identifying Risky Candidates
Not all job candidates are transparent about their digital activities. A Cyber Background Check helps hiring managers identify individuals who may pose a risk to the company’s cybersecurity, allowing businesses to avoid hiring potentially harmful candidates.
2. Strengthening Cybersecurity Practices
By ensuring that employees have passed a Cyber Background Check, businesses can rest assured that their team members will not compromise company data or systems. It creates a culture of cybersecurity awareness within the organization, helping to prevent cyber incidents.
3. Improved Candidate Screening
Traditional background checks might miss important information regarding an applicant’s online behavior, especially in today’s digital age. Cyber Background Checks offer a more comprehensive screening process by uncovering details that are not typically found in conventional background checks.
4. Enhancing Reputation Management
Businesses are increasingly judged based on their cybersecurity standards and practices. By implementing Cyber Background Checks, companies send a strong message to their clients and stakeholders that they prioritize data security, which can enhance their reputation.
Best Practices for Implementing a Cyber Background Check
Implementing a Cyber Background Check requires careful planning and execution. Here are some best practices for businesses:
- Define Clear Guidelines: Establish clear guidelines on what constitutes acceptable online behavior for your employees. This includes defining parameters for evaluating social media activity, online behavior, and potential risks.
- Choose the Right Provider: Partner with reputable cybersecurity firms or services that specialize in conducting Cyber Background Checks. Make sure the provider follows ethical guidelines and legal frameworks to protect both your business and the candidates being checked.
- Transparency and Consent: Always obtain consent from job candidates before conducting a Cyber Background Check. It’s essential to ensure transparency throughout the process and inform candidates of the areas being reviewed.
- Use Results Wisely: When reviewing the results of a Cyber Background Check, don’t make decisions based solely on one red flag. Consider the context and overall risk before making any employment decisions.
The Role of Cyber Background Checks in Preventing Data Breaches
Data breaches are a growing concern for businesses, especially as cybercriminals become more sophisticated. A Cyber Background Check helps prevent data breaches by ensuring that individuals with access to sensitive information or systems do not have a history of behavior that could compromise security. This proactive approach minimizes the chances of insider threats, which are often the root cause of many data breaches.
How to Incorporate Cyber Background Checks into Your Hiring Process
To effectively incorporate Cyber Background Checks into your hiring process, follow these steps:
- Create a Cybersecurity Policy: Establish clear policies on cybersecurity and employee behavior that align with the needs of your business.
- Integrate the Check into the Recruitment Process: Add the Cyber Background Check as a standard step in your recruitment process for roles with access to sensitive information or systems.
- Review Regularly: Since the digital landscape is constantly evolving, consider conducting periodic checks on employees who handle critical data to ensure ongoing security.
Conclusion: A Necessity for Modern Businesses
As cybersecurity threats continue to evolve, businesses must adapt their hiring processes to safeguard their assets and information. A Cyber Background Check is not just a precaution but a necessary step to protect against insider threats, ensure compliance, and strengthen your overall cybersecurity posture. By implementing these checks, businesses can significantly reduce their vulnerability to cybercrime and protect both their data and reputation.


Post Comment